When running vSphere 6 deployments in default (recommended) mode, VMware Certificate Authority is its own root certificate authority. Everything fine and secure with this configuration, but your browser displays a warning because the root certificate is not trusted.

I've written a little script (VBS) that pulls the CA certificate from a vCenter Server and adds it to the local trusted root certificates store. When the root CA is trusted, browser warnings are gone.
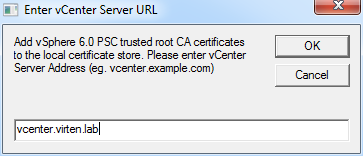
Just save the source to a file with a .vbs extension, or download the .zip package which includes the file. The script asks vor the vCenter FQDN, pulls the certificate archive, unzips it and adds the certificate to the local root store.
Note: Adding certificates to the root store requires administrative permissions.
![]()
Source
Set objFSO = CreateObject("Scripting.FileSystemObject")
Set objApp = CreateObject("Shell.Application")
Set objShell = CreateObject("WScript.Shell")
dim vCenterName
vCenterName = inputbox("Add vSphere 6.0 PSC trusted root CA certificates to the local certificate store. Please enter vCenter Server Address (eg. vcenter.example.com)", "Enter vCenter Server URL", "")
if vCenterName = "" then
wscript.quit
end if
CaCert = "./" & vCenterName & "-cacert.zip"
CaDir = "./" & vCenterName & "-cacert/"
Set newDIR = objFSO.CreateFolder( CaDir )
const SXH_SERVER_CERT_IGNORE_ALL_SERVER_ERRORS = 13056
dim xHttp: Set xHttp = createobject("MSXML2.ServerXMLHTTP")
dim bStrm: Set bStrm = createobject("Adodb.Stream")
xHttp.Open "GET", "https://" & vCenterName & "/certs/download", False
xHttp.setOption 2, SXH_SERVER_CERT_IGNORE_ALL_SERVER_ERRORS
xHttp.Send
with bStrm
.type = 1
.open
.write xHttp.responseBody
.savetofile CaCert, 2
end with
Set unzip=objApp.NameSpace(objFSO.GetAbsolutePathName(CaCert)).Items()
objApp.NameSpace(objFSO.GetAbsolutePathName(CaDir)).copyHere unzip, 16
CertFolder = CaDir & "certs/"
Set objFolder = objFSO.GetFolder(CertFolder)
Set colFiles = objFolder.Files
For Each objFile in colFiles
objShell.run "certutil.exe -addstore Root "& CertFolder & objFile.Name
Next
Download: add-vcenter-root-ca.zip
If you don't want to use the script, you can also follow the instructions in KB2108294 which explains the same procedure.