This post explains how you can hide a VMware based Virtual Machine from designated users or the entire vCenter Server infrastructure. I'am explaining different scenarios where you can hide Virtual Machines including:
- Hide Virtual Machines from Groups or Users in vCenter
- Hide Virtual Machines from the entire vCenter Server
- Hide Virtual Machines from root on Single ESXi instances
- Find hidden Virtual Machines
To clarify, this post does not cover techniques to cloak that the Guest OS is running on a virtual machine, instead of bare metal.
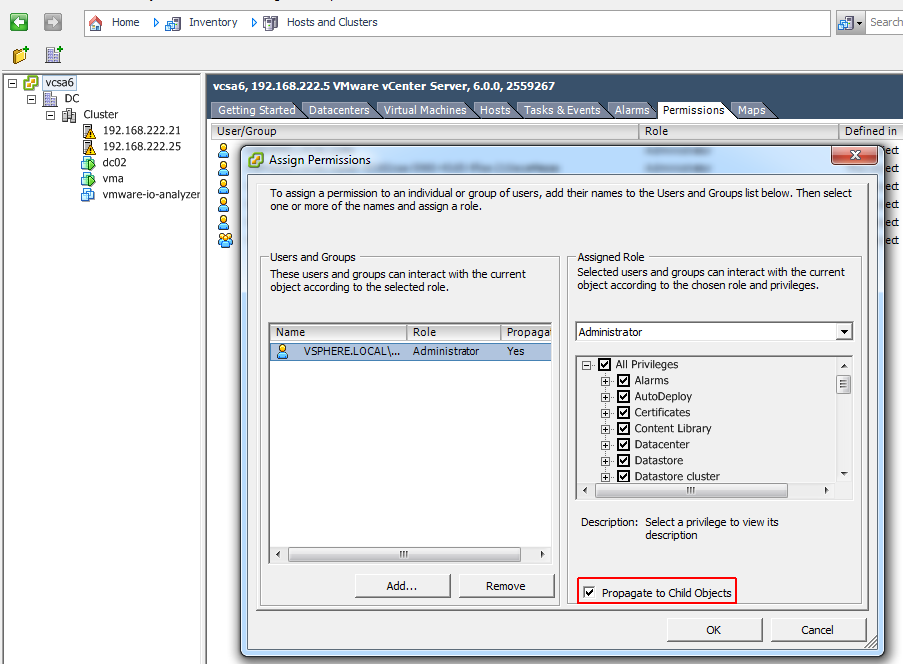
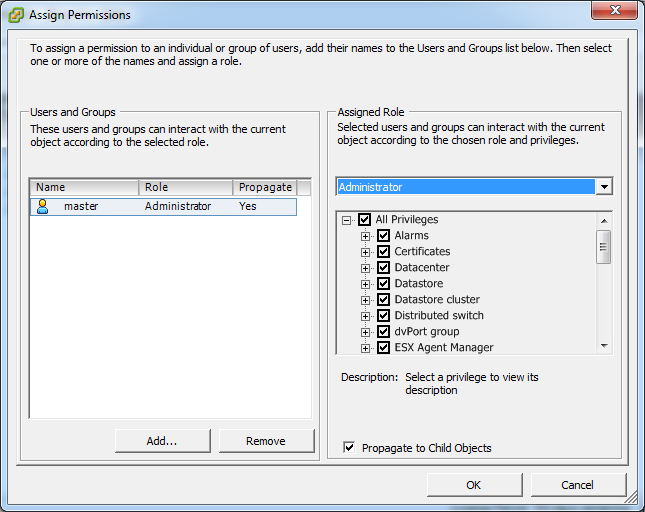
VMware vCenter has a complex authorization management based on roles and permissions. Typically you create User Groups and Roles, and assign permissions to vCenter objects. The easiest and most common method is to assign permissions to the vCenter Server object and propagate them to child objects. This will create global permissions for the user.
Hide Virtual Machines from Groups or Users in vCenter
In some scenarios you might want to revoke access to a single Virtual Machine and thus hide it from the user, without changing the entire permission design. This can be useful for sensitive virtual machines that you want to hide from a designated user or group. Of course, this isn't best practice and there are better ways to do it, but it can be a quick solution. I also remember a bug with an external backup software that crashed while browsing the configuration from a Virtual Machine with an odd configuration. To workaround the issue, the Virtual Machine was hidden for the backup user.
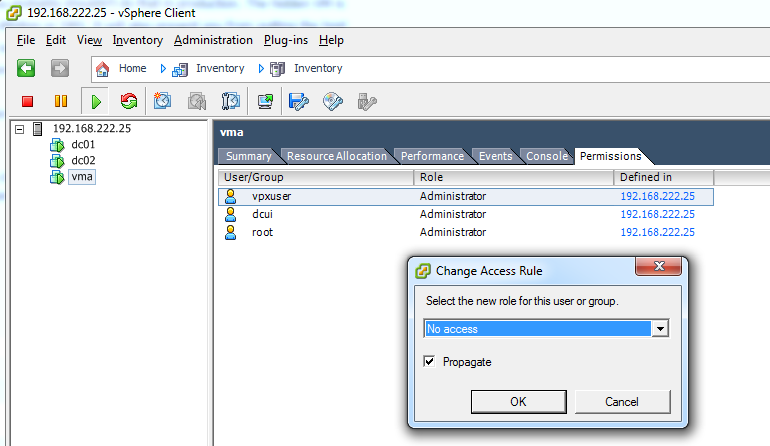
To revoke access and make the VM invisible, you simply have to assign the "No access" role to the Virtual Machine object.
- Navigate to the Virtual Machine
- Open the Permissions tab
- Right Click and select Add Permissions...
- Assign the No Access Role to the user you want to hide the Virtual Machine from

- Press OK
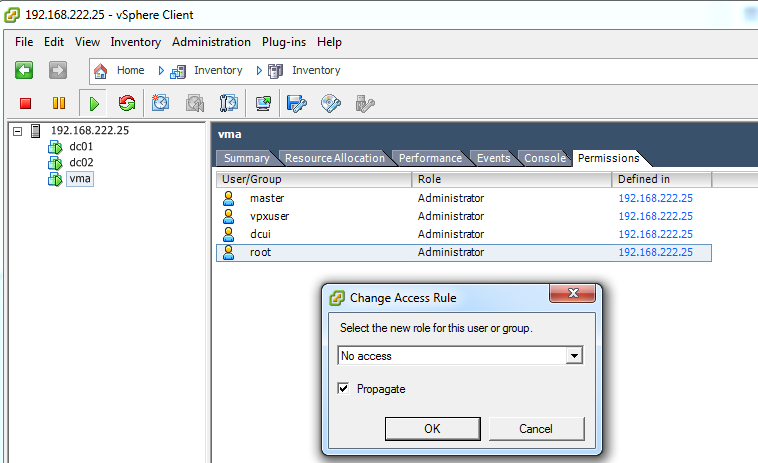
The permission is now changed for the Virtual Machine. Note the "Defined in" column where you can see where the permission has been configured:
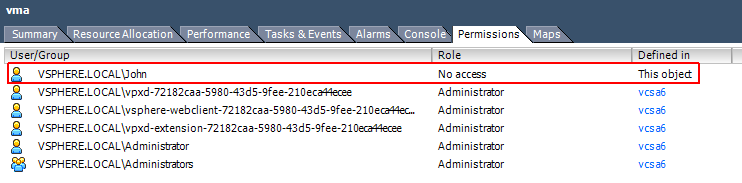
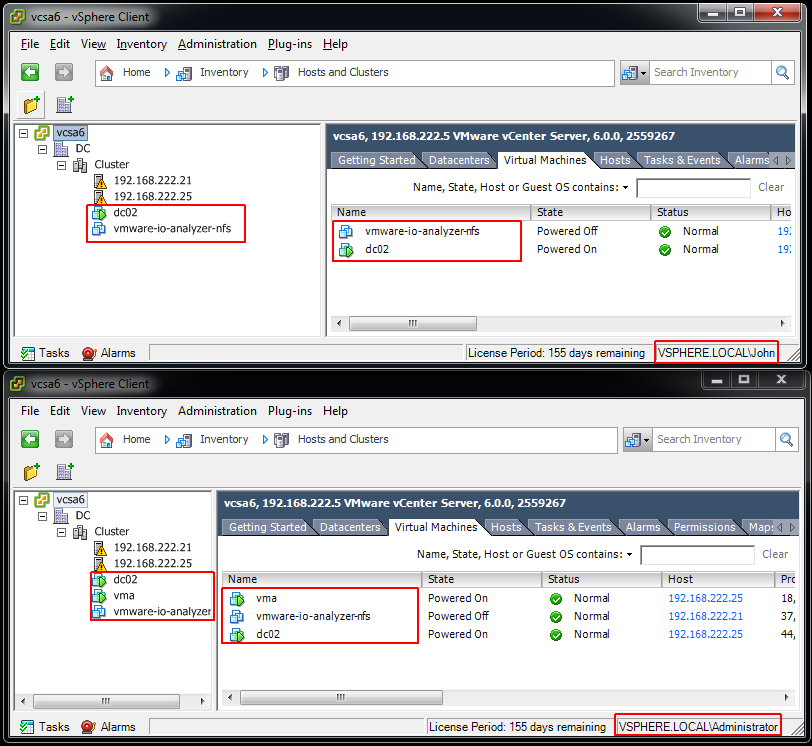
The Virtual Machine (vma) is no longer visible for the user John, but still visible for the Administrator:
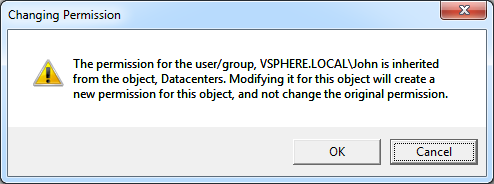
Additional Information: You can also change permissions on objects by double-clicking it in the Permissions tab. You will receive a warning stating that it is creating a new permission:
Hide Virtual Machines from the entire vCenter Server
Another scenario might be when your want to completely hide a Virtual Machine from the vCenter Server. There are not many use cases for that and you probably shouldn't do that in production. The hidden VM is not HA protected and can't be migrated with vMotion or DRS. It will also prevent you from putting the host into maintenance mode. I've used this "trick" some time ago to keep the vCenter clean while I was creating a vSphere Storage Appliance similar deployment for a proof of concept.
To hide a Virtual Machine from the vCenter Server you can revoke access for the vpxuser on the ESXi hosts.
- Use the vSphere Client to connect to the ESXi host as root
- Select the Virtual Machine that you want to hide
- Open the Permission tab
- Double-Click the vpxuser
- Select the No access role and press OK
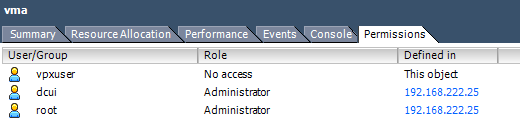
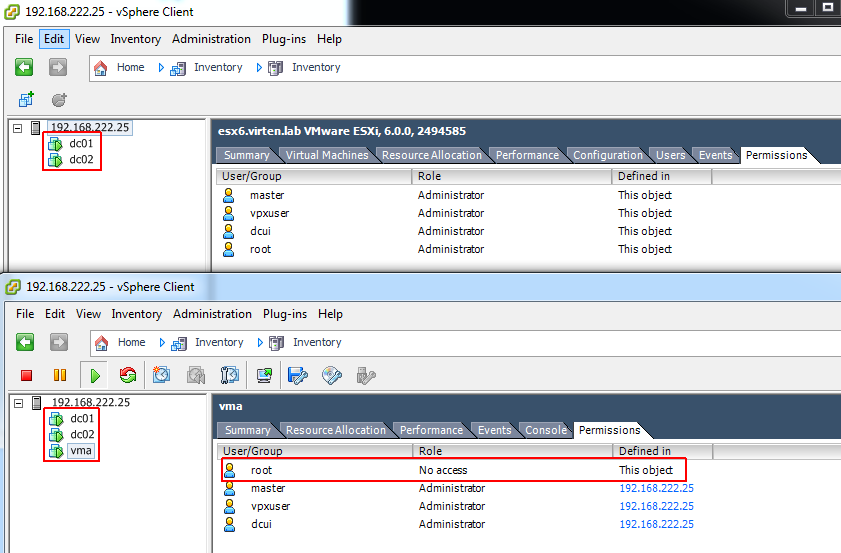
The Virtual Machine (vma) is now completely hidden from the vCenter Server. Depending on the current state, the VM is sometimes detected as orphaned when the vpxuser permission is revoked. You can remove the orphaned object and the VM will continue to run on the local ESXi host.
Of course, no vCenter functionality works for the VM. When you put the host into maintenance mode for example, the process will stuck because it can't see and migrate the machine.
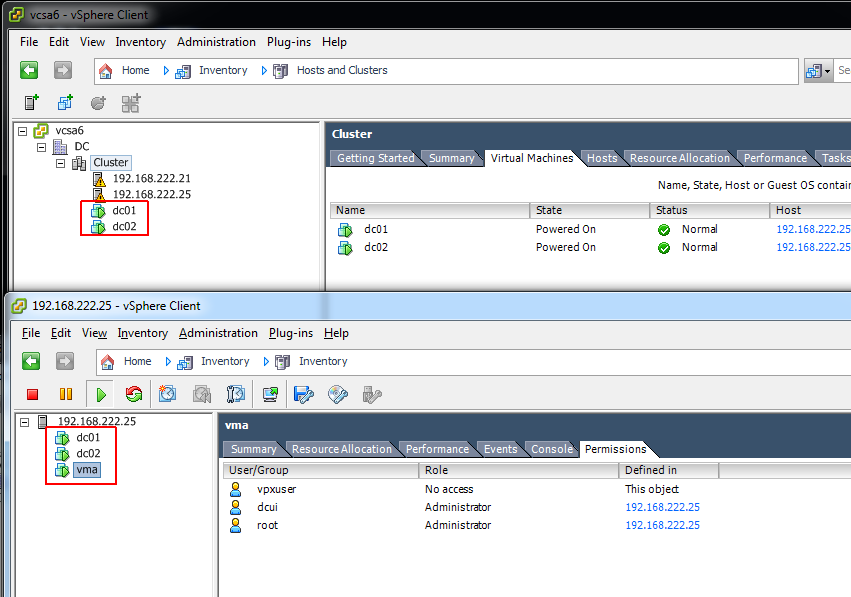
Hide Virtual Machines from root on Single ESXi instances
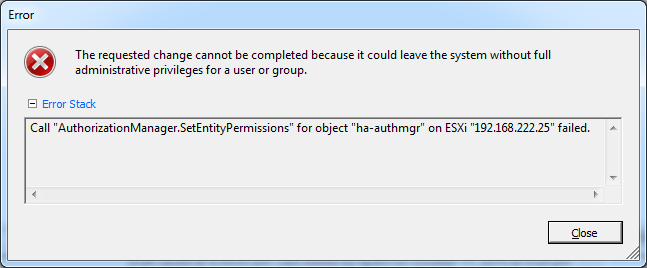
When you are working with a single ESXi host it is possible to hide a Virtual Machine from the root user. You will typically not see this in production and the only use case is probably a malicious behavior, but you should be aware that it is actually possible.
As a security precaution, the ESXi does not allow to remove root permission by default. When you try to remove a root permission, you see the following error message:
Call "AuthorizationManager.SetEntityPermissions" for object "ha-authmgr" on ESXi "192.168.222.25" failed.
To solve this, create a local user with full administrative privileges, a then remove root access:
- Use the vSphere Client to connect to the ESXi host as root
- Open the Users tab and add a new User
- Open the Permissions tab and assign the user the Administrator Role
- You can now configure the No access rule on the VM for root
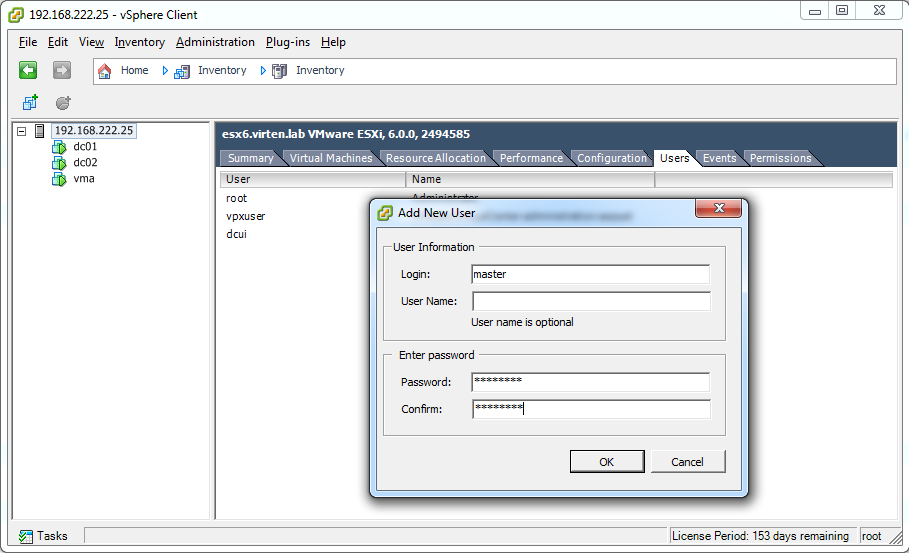
As you can see in the upper picture, the Virtual Machine is no longer visible for the root user. The bottom picture is the view of the newly created user that still has access to the Virtual Machine.
Find hidden Virtual Machines
To find Virtual Machines you first have to know that something is wrong. If you want to make sure that there are no hidden VMs, connect to the ESXi host directely. If you can't put a host into maintenance mode for example you usually connect to the host to see what's wrong. At this point you can quickly identify the problem.
A little bit harder to identify the issue is when the access is revoked for the root user on the local ESXi host. At this point you also can't login with SSH to the host to use esxcli to identify running virtual machines. I don't exactly know why, but when you configure the No access role on any object, the root user is kicked out of the SSH session and can no longer login. The fix is quite simple: Use root to create a new user and give it full access. As there is no "No Access" role on any object for the new user, you can see the hidden VM.
What happens when both users, root and vpxuser do not have access? At this point PowerCLI is your friend. It allows you to run esxcli commands on the ESXi host, while connected to the vCenter server. Here is the output, including the hidden VM (vma):
PowerCLI C:\Users> $esxcli = Get-EsxCli -VMhost 192.168.222.25 PowerCLI C:\Users> PowerCLI C:\Users> $esxcli.vm.process.list() ConfigFile : /vmfs/volumes/54e5567a-e05559ab-66e7-b8aeed72317b/dc01/dc01.vmx DisplayName : dc01 ProcessID : 0 UUID : 56 4d 52 4d 53 00 fb f6-ff 90 dc 66 0b 04 06 a9 VMXCartelID : 433715 WorldID : 433716 ConfigFile : /vmfs/volumes/54e5567a-e05559ab-66e7-b8aeed72317b/dc02/dc02.vmx DisplayName : dc02 ProcessID : 0 UUID : 42 3d db 5f c0 be 5b 65-ec 61 2c ed 68 2d 2b 0b VMXCartelID : 433723 WorldID : 433725 ConfigFile : /vmfs/volumes/54e5567a-e05559ab-66e7-b8aeed72317b/vma/vma.vmx DisplayName : vma ProcessID : 0 UUID : 56 4d 1c ff 7b 64 13 28-b5 83 dc 49 2f fe 50 a5 VMXCartelID : 433733 WorldID : 433734
Great, that's what I wanted to know for a long time :) Thank you
Great article! Thanks!
GRAT !
Thanks man !